Bitcoin wallet on more than one computer
Without his approval, a second withdrawal was made to an unknown address, emptying his wallet of the remaining 1. Although Frank was the victim of theft, the route of attack was not his computer or network. It was the paper wallet he threw into the recycling bin. Unknown to Frank, the paper wallet was taken from the recycling bin by Eve, a dishonest coworker.
Eve added the private key to a custom program that automatically detects deposits into a list of watched addresses, and then withdraws them immediately. MultiBit, working as designed, used the imported paper wallet address to receive 1.
Frank cannot recover the funds, nor is he likely to determine the identity of the thief. Although the examples in the previous section resulted in complete loss of funds, the same mechanisms also allow for partial loss. These conditions were assumed, which may or may not hold at the time a change address problem arises:. For example, a single address that receives multiple payments will contain multiple unspent outputs. Likewise, wallet balances can become distributed across multiple change addresses as the user spends funds.
As expected, her wallet balance decreases to 9 BTC. After installing a new hard drive and restoring her wallet backup, Alice notices something odd. Before the hard drive crash, her wallet balance was 9 BTC. But the balance only read 8 BTC after recovering the backup.
Why does 1 BTC seem to be missing? Alice was using a random address pool wallet, in which Address 2 was not contained in her original backup. In a sense, Alice was lucky because she could have lost her entire wallet balance. On the other hand, without understanding change addresses, Alice would likely be very confused about what happened to the missing 1 BTC.
The same mistake could happen again. When used correctly, change addresses help prevent the identities and spending histories of Bitcoin users from being made public. But with this capability comes the potential for loss and theft.
To avoid potentially costly mistakes, familiarize yourself with change addresses and how your wallet software implements them. The Debit Card from Hell Imagine paying for groceries with a debit card. Bitcoin is Electronic Cash The similarities between Bitcoin and cash run deep. A Bitcoin address can be thought of as the digital equivalent of a cash envelope.
Alice may not re-spend the 10 BTC. Alice pays Bob 5 BTC. Change Address with Multiple Outputs. Alice pays Bob 8 BTC. Change Address is Sender. Change is returned to the sending address. The intended payee is unambiguous. Change Address is not Sender. Change is returned to a newly-created change address. The intended payee is ambiguous. Wallets and Change Addresses Although change addresses play a key role in improving privacy, wallet developers can implement this feature in a number of ways.
Single-Address Wallets use a single address to receive both payments and change. Additional addresses may added when a receiving address is manually added, or a private key is imported. Random Address Pool Wallets use a fixed-size pool of randomly-generated addresses.
Change is sent to the next available empty address, causing the creation of a new empty address to take its place. The best-known example is Bitcoin-Qt.
Deterministic Address Pool Wallets contain a practically infinite pool of deterministically-generated addresses. A subset of this pool contains addresses reserved for receiving change. Examples include Electrum and Armory. Hybrid Wallets use multiple strategies, depending on context. MultiBit, Mycelium , and Electrum are examples.
Preventing and Recovering from Change Address Disasters Incorrect use of Bitcoin change addresses account for many cases of loss or theft of funds. Backup Failure Alice uses Bitcoin-Qt. Count the number of manually-created addresses and spending transactions since your last backup.
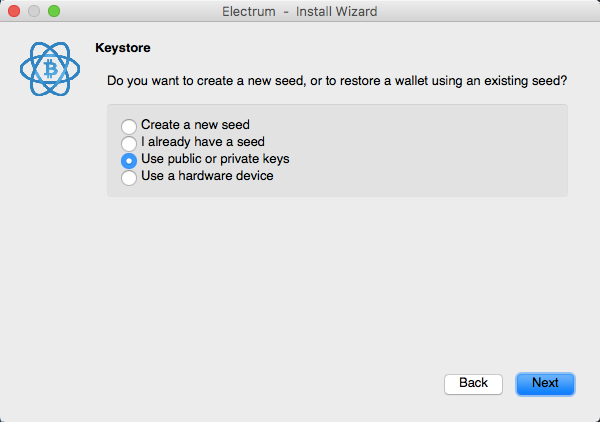
If this number is greater than about 80, back up again. Weekly backups might be enough for most users. Set a very high value e. Using data recovery tools, Alice may be able to salvage the Bitcoin-Qt wallet from the faulty hard drive, and with it her lost funds. Bob uses Electrum to send infrequent bitcoin payments. Worried about possible theft, he wanted a way to keep an eye on his bitcoin balance from one of his many devices.
Bob decided on blockchain. A few weeks later, Bob made a 0. After receiving his merchandise, Bob decided to check his balance with blockchain. Disturbingly, Bob discovered that part of his Overstock payment was transferred to an unknown address. Thinking that his computer running Electrum had been compromised, Bob re-formated the hard drive.
This cleared the balance from the sending address, the only one Bob was monitoring. Electrum encourages the storage of its word address generation seed in a safe location. Should Bob still have access to the seed, he can re-generate his old wallet and recover the change from the Overstock transaction. Carlos is a saver. One day Carlos noticed a deal on new laptops at Overstock and decided to pay using one of his saved bitcoins. But Carlos had a problem: After paying Overstock, he exited the program.
Carlos was worried about leaving any trace of his private key on his computer, so he securely deleted MultiBit and its data directory. He then returned his paper wallet to its safe location. To his shock, the balance read zero. Nineteen bitcoins were sent to an unfamiliar address on the same day as the Overstock payment.
The 19 missing bitcoins were sent to a change address, leaving his paper wallet empty. In securely deleting the MultiBit data directory, Carlos lost any chance of recovering the missing funds. Dave runs Bitcoin-Qt on two computers, a laptop and a desktop in his garage.
Wanting to use both computers to make payments, Dave copied a clean wallet. After making many payments without a problem from both computers, Dave noticed something odd one day.
His laptop wallet showed a zero balance, but his desktop wallet showed the correct balance. Instead, his copy of Bitcoin-Qt running on the desktop used the last available pool address held jointly with the laptop. Back up the wallets on both the laptop and the desktop. Export all private keys from both computers, and sweep them into a new wallet.
Frank received a paper wallet containing 2 BTC as a gift at a company event. Not seeing a need to keep the paper wallet, Frank threw it into the recycling bin at his office. Over time, Frank depleted his Bitcoin funds. Shortly thereafter, Frank bought a set of sheets from Overstock for 0. Although this payment confirmed without issue, Frank noticed something odd.
Without his approval, a second withdrawal was made to an unknown address, emptying his wallet of the remaining 1. Although Frank was the victim of theft, the route of attack was not his computer or network. It was the paper wallet he threw into the recycling bin.
Unknown to Frank, the paper wallet was taken from the recycling bin by Eve, a dishonest coworker. Eve added the private key to a custom program that automatically detects deposits into a list of watched addresses, and then withdraws them immediately. MultiBit, working as designed, used the imported paper wallet address to receive 1.
Frank cannot recover the funds, nor is he likely to determine the identity of the thief. Although the examples in the previous section resulted in complete loss of funds, the same mechanisms also allow for partial loss.
These conditions were assumed, which may or may not hold at the time a change address problem arises:. For example, a single address that receives multiple payments will contain multiple unspent outputs. Likewise, wallet balances can become distributed across multiple change addresses as the user spends funds.
As expected, her wallet balance decreases to 9 BTC. After installing a new hard drive and restoring her wallet backup, Alice notices something odd. Before the hard drive crash, her wallet balance was 9 BTC.
But the balance only read 8 BTC after recovering the backup. Why does 1 BTC seem to be missing? Alice was using a random address pool wallet, in which Address 2 was not contained in her original backup. In a sense, Alice was lucky because she could have lost her entire wallet balance. On the other hand, without understanding change addresses, Alice would likely be very confused about what happened to the missing 1 BTC. The same mistake could happen again.
Everything is done directly on device: PIN entry, seed configuration, transaction validation. There is no need for an additional security card like for the Nano or HW.
The Ledger Unplugged is the contactless version of the Ledger Nano. It is a Java Card-based Fidesmo smart card with the same properties and level of security than the Nano.
But instead of being connected through USB port, Ledger Unplugged is suited to a mobile use with your compatible Android smartphone, thanks to Near Field Communication technology. By initializing the second USB dongle with the same seed as the first one, you'll have two perfectly cloned Ledger Nano. Ideal for an instant backup stored in a safe , or to have copies in different locations.
It has exactly the same properties and level of security, and from the usage point of view it is exactly the same thing. If you order a Ledger HW. For the Enterprise pack, you'll get 10 full HW.
The key form factor is the main difference between the two products. Also, you'll get the HW. Other hardware wallets do not rely on smartcards and are based on regular microcontrollers. This leads to possible security holes such as side channel attacks, private keys leaks through code exploits and physical key extraction as soon as it is stolen. Cold storage such as a paper wallet in a physical safe can be a very effective solution to secure your bitcoins.
The benefit of Ledger Wallet is that it keeps the same level of security but adds convenience. Indeed, cold storage prevents by definition all usage of your bitcoins. As soon as you need to spend them, you'll have to import your private keys on your computer, and you'll have the same security problem if it has been compromised.
The difference, apart from interfaces and functionalities, is that even if your private keys may be stored encrypted on your computer or cloud service , they must be available in plain text in your computer memory whenever you sign transactions. When your computer is compromised by specialized Bitcoin-targetting malware and it is just a matter of time , it will be extremely easy for the malware to steal your bitcoins.
Centralized services host your bitcoins.