Kate spade rachelle bag review
23 comments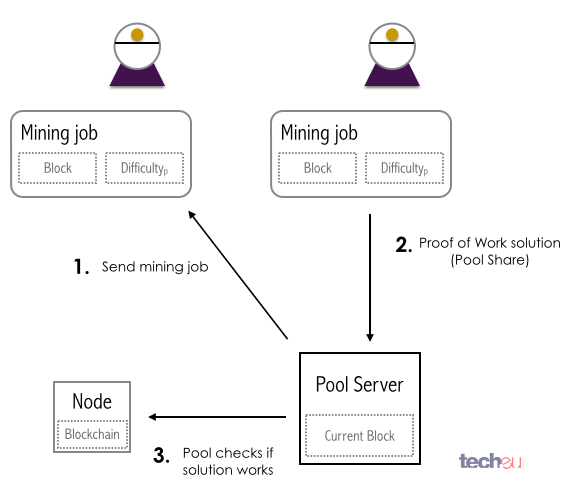
Bitcoin growth with hybrid bot joints
A proof-of-work PoW system or protocol , or function is an economic measure to deter denial of service attacks and other service abuses such as spam on a network by requiring some work from the service requester, usually meaning processing time by a computer. The concept was invented by Cynthia Dwork and Moni Naor as presented in a journal article.
A key feature of these schemes is their asymmetry: Proof of space PoS proposals apply the same principle by proving a dedicated amount of memory or disk space instead of CPU time. Proof of bandwidth approaches have been discussed in the context of cryptocurrency. Proof of ownership aims at proving that specific data are held by the prover. One popular system, used in Hashcash , uses partial hash inversions to prove that work was done, as a good-will token to send an e-mail.
For instance the following header represents about 2 52 hash computations to send a message to calvin comics. It is verified with a single computation by checking that the SHA-1 hash of the stamp omit the header name X-Hashcash: Whether POW systems can actually solve a particular denial-of-service issue such as the spam problem is subject to debate; [3] [4] the system must make sending spam emails obtrusively unproductive for the spammer, but should also not prevent legitimate users from sending their messages.
In other words, a genuine user should not encounter any difficulties when sending an email, but an email spammer would have to expend a considerable amount of computing power to send out many emails at once. Proof-of-work systems are being used as a primitive by other more complex cryptographic systems such as bitcoin which uses a system similar to Hashcash. Known-solution protocols tend to have slightly lower variance than unbounded probabilistic protocols, because the variance of a rectangular distribution is lower than the variance of a Poisson distribution with the same mean.
Finally, some POW systems offer shortcut computations that allow participants who know a secret, typically a private key, to generate cheap POWs. The rationale is that mailing-list holders may generate stamps for every recipient without incurring a high cost. Whether such a feature is desirable depends on the usage scenario. Computer scientist Hal Finney built on the proof-of-work idea, yielding a system that exploited reusable proof of work "RPOW".
Just as a gold coin's value is thought to be underpinned by the value of the raw gold needed to make it, the value of an RPOW token is guaranteed by the value of the real-world resources required to 'mint' a POW token. A website can demand a POW token in exchange for service. Requiring a POW token from users would inhibit frivolous or excessive use of the service, sparing the service's underlying resources, such as bandwidth to the Internet , computation, disk space, electricity and administrative overhead.
Finney's RPOW system differed from a POW system in permitting the random exchange of tokens without repeating the work required to generate them. This would save the resources otherwise needed to 'mint' a POW token. The anti-counterfeit property of the RPOW token was guaranteed by remote attestation. Since the source code for Finney's RPOW software was published under a BSD -like license , any sufficiently knowledgeable programmer could, by inspecting the code, verify that the software and, by extension, the RPOW server never issued a new token except in exchange for a spent token of equal value.
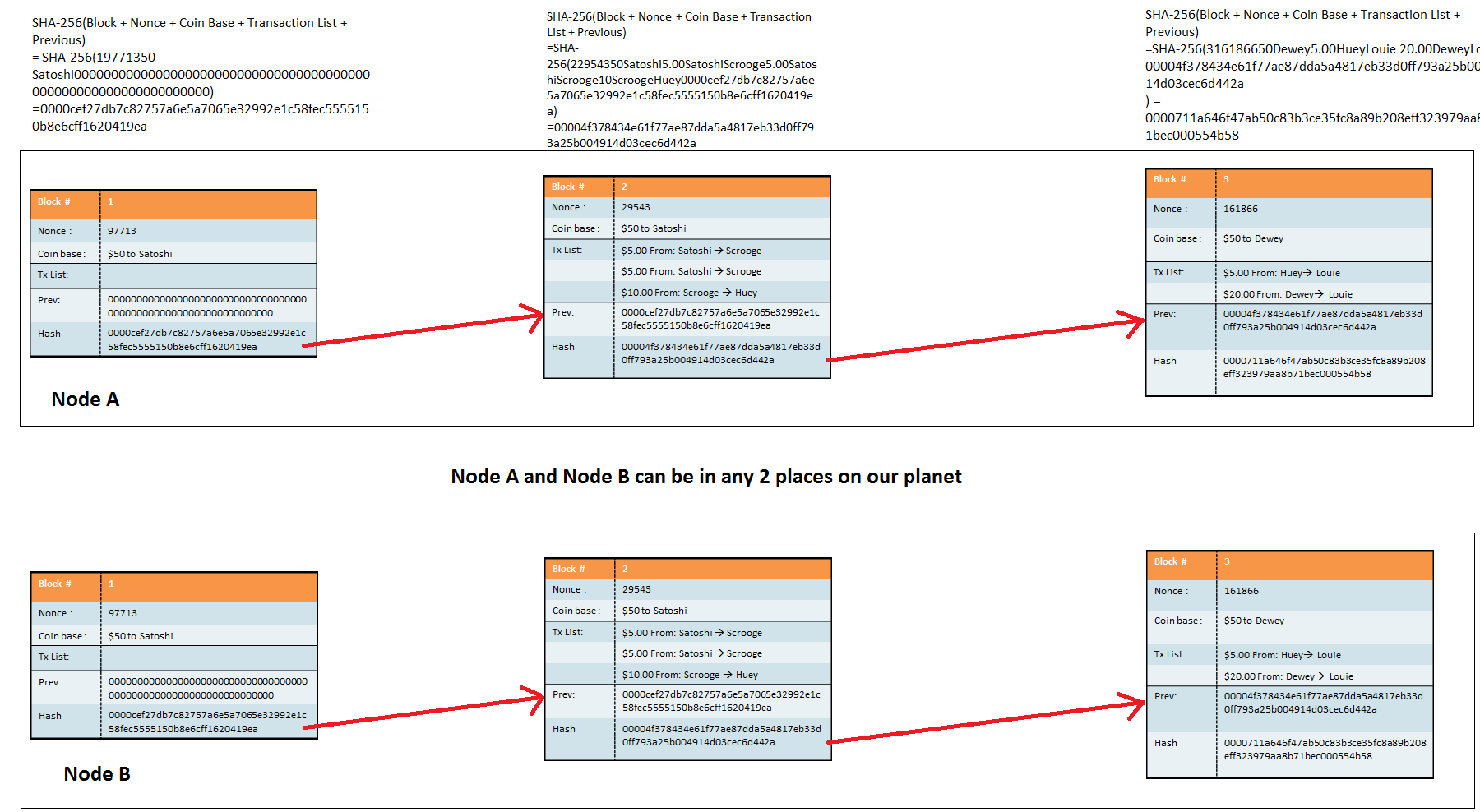
Until , Finney's system was the only RPOW system to have been implemented; it never saw economically significant use. In , the Bitcoin network went online. But in Bitcoin double-spend protection is provided by a decentralized P2P protocol for tracking transfers of coins, rather than the hardware trusted computing function used by RPOW. Bitcoin has better trustworthiness because it is protected by computation. Bitcoins are "mined" using the Hashcash proof-of-work function by individual miners and verified by the decentralized nodes in the P2P bitcoin network.
The difficulty is periodically adjusted to keep the block time around a target time. Many POW systems require the clients to do useless work, such as inverting a hash function. This means that a lot of resources mainly the electricity that powers the clients' computers is used only for providing trust in the currency. To be more efficient with that resource expenditure, some alternative coins use a POW system where the performed work is actually useful. For example, Primecoin requires clients to find unknown prime numbers of certain types, which can have useful side-applications see Primecoin Proof-of-work system.
From Wikipedia, the free encyclopedia. This article may require cleanup to meet Wikipedia's quality standards. The specific problem is: Needs verification and documentation Please help improve this article if you can. May Learn how and when to remove this template message. Lecture Notes in Computer Science No. Communications and Multimedia Security. Cryptology ePrint Archive, Report. Financial Cryptography and Data Security: First announce in March Updated version May 4, A cryptographic defense against connection depletion attacks".
Archived from the original on December 22, History Economics Legal status. List of bitcoin companies List of bitcoin organizations List of people in blockchain technology. Proof-of-authority Proof-of-space Proof-of-stake proof-of-work. Dogecoin Gulden Litecoin PotCoin. Dash Decred Primecoin Auroracoin. IO Gridcoin Nxt Waves. Anonymous Internet banking Bitcoin network Complementary currency Crypto-anarchism Cryptocurrency exchange Digital currency Double-spending Electronic money Initial coin offering Airdrop Virtual currency.
Retrieved from " https: Articles needing cleanup from May All pages needing cleanup Cleanup tagged articles with a reason field from May Wikipedia pages needing cleanup from May Wikipedia articles needing clarification from February Webarchive template wayback links. Views Read Edit View history. This page was last edited on 11 April , at By using this site, you agree to the Terms of Use and Privacy Policy.