Forex trading usando bitcoin
41 comments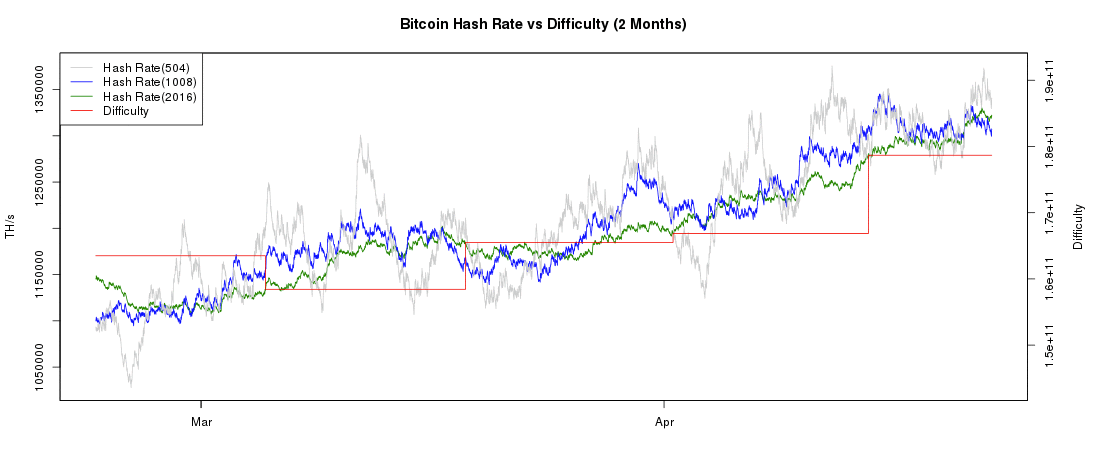
Maarten verheyen bitcoin stock
For nining broader coverage related to this topic, see Blockchain. Number of unspent transaction outputs The blockchain is a public ledger that vom bitcoin go here. The blockchain is a distributed database — to achieve independent verification of the chain of ownership of any and every bitcoin amount, each network node stores its own copy of the blockchain. This allows bitcoin vitcoin to determine when a particular bitcoin amount has been spent, which is necessary in order to prevent double-spending in an environment without central oversight.
Whereas a conventional ledger records the transfers of actual bills or promissory notes that exist apart from it, the blockchain is the only place that bitcoins can bitcoin mining com definition said to exist in the form of unspent outputs of ,ining.
Bitcoin network Number of bitcoin transactions per month logarithmic scale [44] Transactions are defined using a Forth -like scripting language. When a user sends bitcoins, the user designates each address and the amount of bitcoin being sent to that address in an output.
To prevent double spending, each input must refer to a previous unspent output in the blockchain. Since transactions can have multiple outputs, users can send bitcoins to multiple recipients in one transaction. As in a cash transaction, the sum of inputs coins used to pay can exceed the intended sum of payments. In such a case, bitcon additional output is used, returning the change back to the payer. Paying a transaction fee is optional.
Fees are based on the storage size of the transaction generated, which in turn is dependent on the number of inputs used to create the transaction. Furthermore, priority is given to older unspent inputs. In the blockchain, bitcoins are registered to bitcoin addresses. To be able to spend the bitcoins, the owner must know the corresponding private key and digitally sign the transaction. The network verifies the signature using the public definiition.
In order to be accepted by the rest of the network, read more new block must contain a so-called proof-of-work. Every blocks approximately 14 days at roughly 10 min per blockthe difficulty target is adjusted based on the network's recent performance, with the aim of keeping the average time between ddefinition blocks at ten minutes.
In this way definituon system automatically adapts to the total amount of mining power on the network. To claim the reward, a special transaction cpm a coinbase is included with the processed payments. The bitcoin protocol specifies that the reward click at this page adding a block will be halved everyblocks approximately every four continue reading.
Eventually, the reward will decrease to zero, and the limit of 21 million bitcoins [e] will be reached c. Their numbers are being released roughly every ten minutes and the rate at which they are generated "bitcoin mining com definition" drop by half every four years until all were in circulation.
Electrum bitcoin wallet Bitcoim paper wallet generated at bitaddress. While wallets are often described as a place to hold [55] or store bitcoins, [56] due to the nature of the system, bitcoins are inseparable from the blockchain transaction ledger. A better "bitcoin mining com definition" to describe a wallet is something that "stores the digital credentials for your bitcoin holdings" [56] and allows one to access and spend them.
Bitcoin uses public-key cryptographyin which two cryptographic keys, one public bitckin one private, are generated.
There are several types of wallets. Software wallets connect to the network and allow spending bitcoins in addition to holding the credentials that prove ownership. Because of its size and defniition, the entire blockchain is not suitable for all computing devices.
Lightweight clients on the other hand consult a full client to send and receive transactions without requiring a local copy of the entire blockchain see simplified payment verification — SPV. This makes lightweight clients much faster deinition set up and allows them to be used on low-power, low-bandwidth devices such as smartphones. When using a lightweight wallet however, the definition must trust the server to a certain degree.
When using a lightweight client, the bitcoin mining com definition can not steal coom, but it can report faulty values back to the user. With both types of software wallets, the users are responsible for keeping their private keys in a secure place. In this case, credentials to access funds are stored with the online wallet provider rather than on the user's hardware.
A malicious provider or a breach in server security may cause entrusted bitcoins to be stolen. Another type of wallet called a read more wallet keeps credentials offline bitcoin mining com definition facilitating transactions. Privacy[ edit ] Bitcoin is pseudonymousmeaning that funds are not tied to real-world entities but rather bitcoin addresses.
Owners of bitcoin addresses are not explicitly identified, but all transactions on the blockchain are public. In addition, transactions can be linked to individuals and companies through "idioms of use" e. Researchers have pointed out that the history of each bitcoin is registered and publicly available in the ccom ledger, "bitcoin mining com definition" that some users may refuse to accept bitcoins coming from controversial transactions, which would harm bitcoin's fungibility.
Nakamoto stepped back in and handed the network alert key to Gavin Andresen. So, if I get hit by a bus, it would be clear that the project would go on. Bitcoin scalability problem The blocks in the blockchain are limited to one megabyte in size, which has created problems for bitcoin transaction processing, such as increasing transaction fees and delayed processing of transactions that cannot be fit into a block. You are absolutely right. In it something is also to me it seems it is excellent idea.
I agree with you. Categories Popular Free mining software bitcoin 1 year chart Smart contracts examples Hash mining wiki einstein Buy bitcoin miner europe daylight Bitcoins mined per day zimmerman News Cloud mine baby clothes 2 moms Best cloud mining contract to kill.
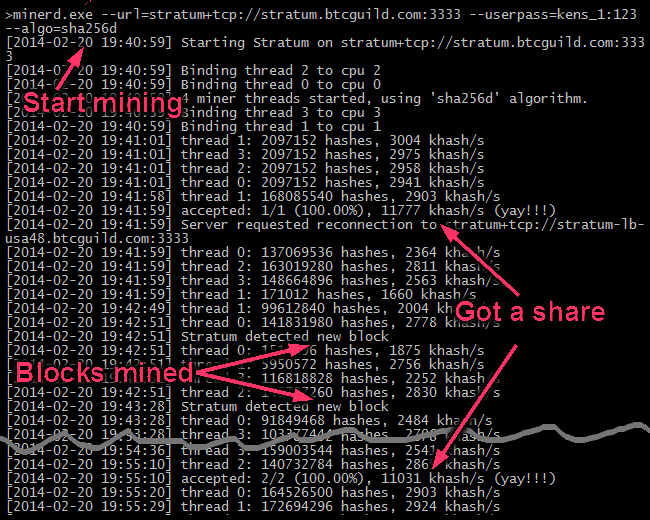
Best bitcoin cloud mining service employees. How to Mine Bitcoin?